Every day, billions of messages, emails, and files travel across the internet. From private conversations to financial details, we share more sensitive information online than ever before. But with major data breaches exposing millions — sometimes billions — of records, protecting digital communication has become essential.
This is where end-to-end encryption (E2EE) comes in. It’s one of the most powerful privacy tools available today. But what exactly does it mean, and why should you care?
Let’s break it down in simple terms.
What Is End-to-End Encryption?
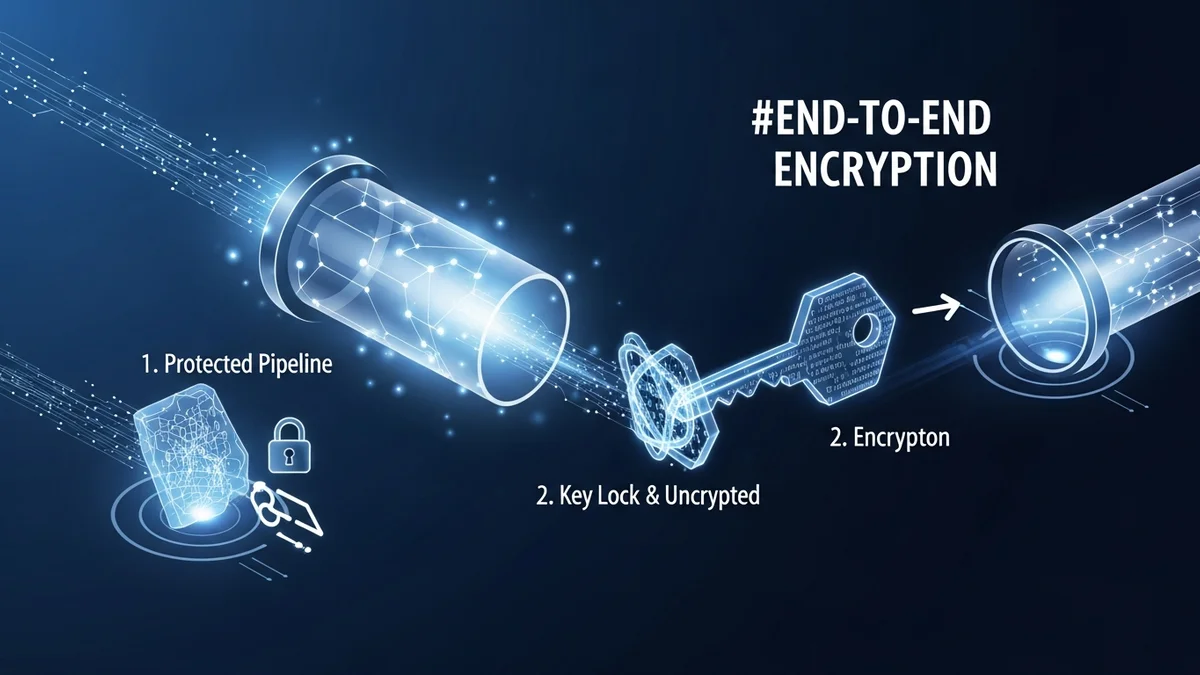
End-to-end encryption is a security method that ensures only the sender and the intended recipient can read a message. No one else — not hackers, not internet service providers, not even the company providing the service — can access the content.
When a message is sent using E2EE, it is encrypted (scrambled) on the sender’s device and can only be decrypted (unscrambled) on the recipient’s device. If someone intercepts the data in transit, all they see is unreadable code.
Popular services that use end-to-end encryption include:
- Signal
- iMessage
- Proton Mail (between Proton users)
Without end-to-end encryption, your messages may still be encrypted in transit, but the service provider often has the keys to decrypt them. That means your data could be accessed internally, handed over, or exposed in a breach.
How End-to-End Encryption Works (In Simple Terms)
End-to-end encryption relies on advanced cryptography, typically using a combination of public and private keys.
- A public key encrypts the message.
- A private key decrypts it.
When you send a message, your device encrypts it using the recipient’s public key. Once delivered, only their private key — stored securely on their device — can unlock it.
Even if attackers intercept the message during transmission (for example, over public Wi-Fi), they cannot read it without the private key.
This differs from basic encryption methods like HTTPS. While HTTPS encrypts data between your browser and a website (and now protects over 95% of web traffic, according to Google’s transparency reports), the website itself can still see and store your information. End-to-end encryption removes that visibility.
Why End-to-End Encryption Matters More Than Ever
Data breaches are not rare events. They are constant.
Consider these well-known examples:
- Yahoo (2013–2014): 3 billion accounts compromised.
- Equifax (2017): 147 million people exposed, including Social Security numbers.
- Facebook (2021): 533 million users’ data leaked online.
When companies store unencrypted or centrally accessible data, they become prime targets. If attackers break in, they can often access readable user information.
End-to-end encryption significantly reduces this risk. Even if a company’s servers are compromised, attackers cannot read encrypted messages without users’ private keys.
However, encryption does not prevent every type of data exposure. If your email address and password are leaked from a non-encrypted database, criminals can still attempt credential stuffing attacks. That’s why tools like LeakDefend are essential — they monitor your email addresses for breaches and alert you if your credentials appear in leaked databases.
What End-to-End Encryption Does Not Protect You From
While E2EE is powerful, it’s not a complete cybersecurity solution.
It does not protect against:
- Weak passwords
- Phishing attacks
- Malware on your device
- Data you voluntarily share
If your device is infected with spyware, attackers may capture messages before they’re encrypted or after they’re decrypted. If you reuse passwords across multiple sites, a single breach can expose multiple accounts.
That’s why a layered security approach works best. Use end-to-end encrypted services, enable two-factor authentication, and actively monitor for data leaks. LeakDefend.com lets you check all your email addresses for free and receive alerts if they appear in known breaches — helping you respond before attackers exploit exposed credentials.
Who Should Use End-to-End Encryption?
There’s a common myth that encryption is only for journalists, activists, or corporations. In reality, everyone benefits from stronger privacy.
You should prioritize end-to-end encryption if you:
- Share financial or banking information
- Discuss sensitive work matters
- Send personal photos or private conversations
- Travel frequently and use public Wi-Fi
- Value digital privacy in general
Cybercrime damages are projected to reach trillions of dollars annually worldwide. Identity theft, account takeovers, and financial fraud often start with exposed personal data. End-to-end encryption reduces the amount of readable information available to criminals.
How to Start Using End-to-End Encryption Today
Adopting E2EE is easier than most people think.
- Use messaging apps like Signal or enable encryption features in WhatsApp.
- Choose email providers that support end-to-end encryption.
- Keep your devices updated to patch security vulnerabilities.
- Use strong, unique passwords with a password manager.
- Enable two-factor authentication wherever possible.
And most importantly, monitor your digital exposure. Even with encryption, past breaches can still put your accounts at risk. Services like LeakDefend help you stay informed by scanning breach databases and notifying you when your information appears.
🔒 Check If Your Email Was Breached — Monitor up to 3 email addresses for free with LeakDefend. Start Your Free Trial →
Conclusion: Encryption Is No Longer Optional
End-to-end encryption is one of the most important privacy innovations of the modern internet. It ensures that your conversations and sensitive data remain accessible only to you and the people you trust.
But encryption is just one layer of protection. Data breaches, leaked passwords, and phishing attacks remain widespread threats. Combining secure communication tools with proactive breach monitoring creates a far stronger defense.
In a world where billions of records have already been exposed, protecting your digital life isn’t paranoia — it’s practical. Use end-to-end encryption wherever possible, stay alert to emerging threats, and regularly check whether your information has been compromised. Your privacy depends on it.