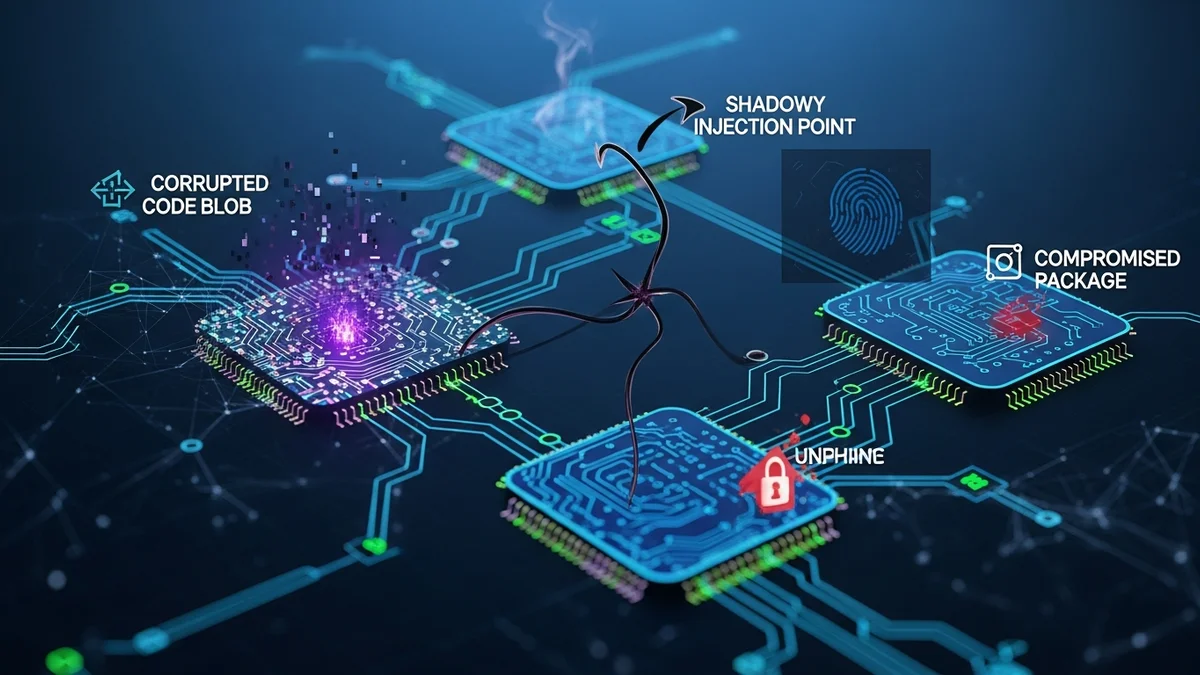
When you install a software update, you probably assume it’s safe. After all, it comes directly from a company you trust. But what if that trusted vendor has already been compromised? That’s the dangerous reality of supply chain attacks—a fast-growing cybersecurity threat where hackers infiltrate legitimate software providers to spread malware to thousands, or even millions, of users at once.
Instead of attacking individuals one by one, cybercriminals compromise the “supply chain” that delivers software, hardware, or services. The result is a highly efficient, stealthy, and devastating method of attack. Here’s how supply chain attacks work, why they’re so effective, and what you can do to reduce your risk.
What Is a Supply Chain Attack?
A supply chain attack occurs when hackers infiltrate a trusted third-party vendor—such as a software developer, IT service provider, or hardware manufacturer—to distribute malicious code to customers.
Rather than breaking into your systems directly, attackers compromise:
- Software update mechanisms
- Open-source libraries and dependencies
- Managed service providers (MSPs)
- Cloud-based platforms
- Hardware firmware or embedded components
Because the malicious code is delivered through legitimate channels, it often bypasses traditional security tools. Users install the infected update believing it’s safe, unknowingly giving attackers access to their systems.
High-Profile Supply Chain Attack Examples
Supply chain attacks aren’t theoretical—they’ve already caused massive damage worldwide.
SolarWinds (2020)
One of the most notorious supply chain attacks in history, the SolarWinds breach affected around 18,000 customers, including U.S. government agencies and Fortune 500 companies. Hackers inserted malicious code into a routine Orion software update. Once installed, it created a backdoor for espionage and data theft. The attack went undetected for months.
Kaseya (2021)
Cybercriminal group REvil exploited vulnerabilities in Kaseya’s VSA software, used by managed service providers. By compromising one vendor, attackers were able to deploy ransomware to up to 1,500 downstream businesses globally.
Log4j (2021)
The Log4j vulnerability wasn’t a traditional breach but a flaw in a widely used open-source logging library. Because Log4j was embedded in millions of applications, the vulnerability created a global supply chain crisis. Organizations worldwide scrambled to patch systems as attackers began exploiting it within days of disclosure.
According to industry reports, supply chain attacks increased by more than 600% between 2020 and 2022, highlighting how attractive this strategy has become for cybercriminals.
Why Supply Chain Attacks Are So Effective
Supply chain attacks succeed because they exploit trust. When software updates come from recognized vendors, they are typically:
- Digitally signed and verified
- Automatically installed
- Whitelisted by security tools
This creates a powerful advantage for attackers. Instead of trying to trick individual users with phishing emails, they compromise a single trusted source and gain access to thousands of networks at once.
Other reasons these attacks are difficult to detect include:
- Delayed activation: Malware may remain dormant for weeks.
- Blended traffic: Malicious communications appear legitimate.
- Deep system access: Software updates often require high-level privileges.
For organizations, this means traditional perimeter defenses are no longer enough. If the attack enters through approved software, detection becomes much harder.
The Hidden Risk to Individuals
While supply chain attacks often make headlines for targeting corporations or governments, individuals are also at risk. If you use popular productivity apps, password managers, antivirus software, or cloud services, you are part of the supply chain ecosystem.
If attackers gain access to:
- User databases
- Email addresses
- Encrypted or hashed passwords
- API keys
- Billing details
Your personal information may eventually surface in data dumps or dark web marketplaces.
This is why proactive breach monitoring is critical. Tools like LeakDefend can monitor your email addresses for breaches and alert you if your data appears in compromised databases. Even if the breach originated from a third-party vendor you barely remember signing up for, you’ll know quickly and can take action.
How to Reduce Your Risk
You can’t control whether a major vendor gets hacked—but you can control how exposed you are when it happens.
1. Use Unique Passwords Everywhere
If one compromised service exposes your password, attackers will test it on other platforms. A password manager helps prevent credential reuse.
2. Enable Multi-Factor Authentication (MFA)
Even if attackers obtain your credentials from a supply chain breach, MFA can block unauthorized logins.
3. Monitor Your Email Addresses
Because most breaches are tied to email accounts, monitoring is essential. LeakDefend.com lets you check all your email addresses for free and receive alerts if they’re exposed in known data breaches.
4. Limit Third-Party App Connections
Review connected apps in your Google, Microsoft, and social media accounts. Remove tools you no longer use.
5. Act Quickly After Breach Notifications
If a company announces a breach, change your password immediately—especially if it’s reused elsewhere.
Why Supply Chain Security Is the Future of Cyber Defense
As software ecosystems become more interconnected, supply chain risk will only grow. Modern applications rely heavily on third-party APIs, open-source components, and cloud infrastructure. A single weak link can cascade across thousands of systems.
Governments are responding. In the United States, executive orders now require stricter software supply chain security standards for federal vendors. Cybersecurity frameworks increasingly emphasize vendor risk management and software bill of materials (SBOM) documentation.
But regulation alone isn’t enough. Organizations must continuously evaluate vendors, audit dependencies, and implement zero-trust principles. Individuals must stay alert and assume that even trusted services can be compromised.
Most importantly, visibility matters. If your data is exposed due to a third-party breach, knowing quickly makes all the difference. Early detection gives you time to change passwords, secure accounts, and prevent identity theft. That’s where services like LeakDefend play a critical role—providing ongoing monitoring so you’re not left in the dark.
🔒 Check If Your Email Was Breached — Monitor up to 3 email addresses for free with LeakDefend. Start Your Free Trial →
Conclusion
Supply chain attacks represent a fundamental shift in cybercrime strategy. Instead of attacking individuals directly, hackers compromise the trusted software and services we rely on every day. From SolarWinds to Log4j, these incidents demonstrate how one breach can ripple across the globe.
You can’t prevent every vendor from being hacked. But you can reduce your exposure, practice strong password hygiene, enable multi-factor authentication, and monitor your accounts for signs of compromise. In a world where even trusted software can become a threat vector, awareness and proactive monitoring are your strongest defenses.
The software you trust should make your life easier—not put your data at risk. Staying informed and prepared is the best way to ensure it stays that way.