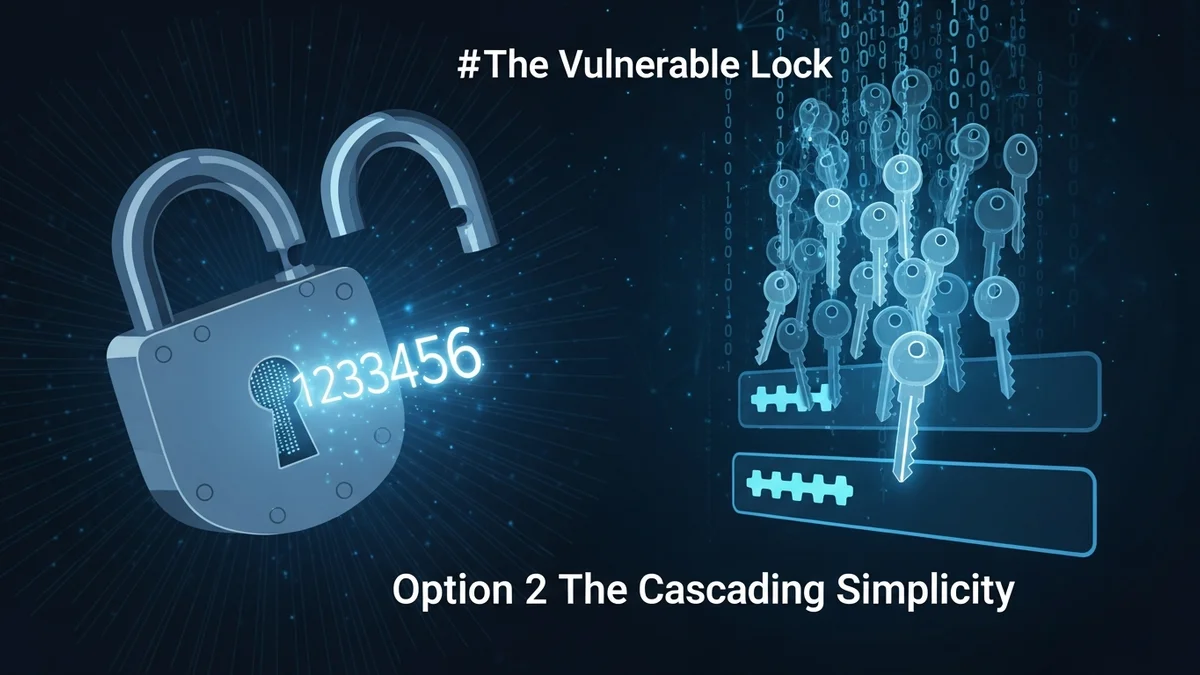
It’s 2026—and “123456” is still the most common password in the world.
Year after year, cybersecurity reports from companies like NordPass and SplashData show the same troubling pattern: millions of people continue to rely on extremely weak, easily guessable passwords. Despite constant headlines about massive data breaches, phishing attacks, and identity theft, the world’s favorite password remains six consecutive digits.
But why? And more importantly, what does this say about the current state of online security?
The Numbers Don’t Lie: Weak Passwords Dominate
Multiple annual password studies consistently rank “123456” at the top. In some reports, it’s been used millions of times across leaked databases. Other common passwords include:
- password
- 123456789
- qwerty
- 111111
- abc123
According to publicly analyzed breach data, many of these passwords can be cracked in less than one second using modern brute-force tools. That means if attackers obtain a hashed password database, accounts protected by “123456” are effectively unlocked instantly.
This isn’t just theory. Major breaches—including LinkedIn (2012), Yahoo (2013–2014), and countless smaller leaks since—have revealed millions of credentials protected by embarrassingly weak passwords. And those are just the breaches we know about.
Why Do People Still Use “123456”?
It’s easy to blame users for laziness. The reality is more complex.
1. Convenience over security. People juggle dozens—sometimes hundreds—of accounts. Simplicity wins when login fatigue sets in.
2. Underestimating risk. Many assume, “It won’t happen to me.” Until it does.
3. Password reuse habits. Even if “123456” isn’t used everywhere, weak variations often are. Attackers exploit this through credential stuffing.
4. Lack of awareness. Not everyone understands how quickly modern cracking tools work.
There’s also a psychological component. Humans prefer patterns. Sequential numbers are easy to remember, type, and recall under stress. Unfortunately, they’re just as easy for attackers to guess.
What This Means in the Age of Data Breaches
Weak passwords are dangerous on their own—but catastrophic when combined with large-scale data breaches.
Every year, billions of credentials are exposed in breaches affecting social networks, online stores, forums, SaaS platforms, and subscription services. Once leaked, these credentials often circulate on dark web marketplaces within days.
Here’s where “123456” becomes especially risky:
- Credential stuffing attacks: Hackers test leaked username/password combinations across other websites.
- Automated login bots: Scripts attempt common passwords at scale.
- Account takeover (ATO): Once inside, attackers change recovery emails and lock victims out.
If you reuse “123456” (or any weak password) across multiple accounts, one breach can domino into many compromised services—including banking, subscription platforms, and even work accounts.
Tools like LeakDefend help mitigate this risk by monitoring your email addresses for exposure in known breaches. If your credentials appear in a leak, you can take action before attackers do.
The Automation Problem: Hackers Don’t Guess—They Calculate
Many people still imagine hackers manually guessing passwords. In reality, attacks are automated and industrialized.
Password-cracking software uses:
- Dictionary attacks (common words and phrases)
- Brute-force attacks (systematic combinations)
- Hybrid attacks (common passwords plus predictable tweaks like “123456!”)
Sequential numbers like “123456” are the first entries in cracking dictionaries. They’re not just weak—they’re guaranteed to be tested immediately.
With modern GPUs and cloud computing, weak passwords can be cracked at billions of guesses per second, depending on hashing algorithms. Even moderately complex passwords can fall quickly if reused or poorly protected.
And once cracked, attackers don’t stop at one account. They escalate privileges, mine personal data, and sometimes sell verified access to others.
Why Passwords Persist Despite Better Alternatives
You might wonder: with passkeys, biometrics, and two-factor authentication (2FA), why are we still talking about “123456”?
Because passwords aren’t going away anytime soon.
While passkeys are growing in adoption, millions of websites still rely on traditional password authentication. Many users don’t enable 2FA even when it’s available. And some legacy systems don’t support modern authentication methods at all.
Until passwordless systems become universal, password hygiene remains essential.
That includes:
- Using unique passwords for every account
- Creating passwords at least 12–16 characters long
- Using a password manager to generate and store credentials
- Enabling multi-factor authentication wherever possible
It also means proactively checking whether your credentials have already been exposed. LeakDefend.com lets you check all your email addresses for free and monitor future breach alerts—helping you stay ahead of attackers instead of reacting after damage is done.
What “123456” Really Reveals About Online Security
The continued dominance of “123456” isn’t just about poor choices. It reveals a deeper issue: usability still conflicts with security.
When security feels complicated, people default to convenience. When platforms don’t enforce strong password policies, weak ones slip through. And when users aren’t alerted quickly after breaches, exposed credentials linger for months—or years.
The good news? Small changes dramatically reduce risk.
A strong, unique password combined with 2FA makes automated attacks exponentially harder. Monitoring your exposure reduces the window of vulnerability. And eliminating password reuse stops credential stuffing in its tracks.
🔒 Check If Your Email Was Breached — Monitor up to 3 email addresses for free with LeakDefend. Start Your Free Trial →
Conclusion: The Real Cost of “Easy” Passwords
“123456” is more than just a weak password—it’s a symbol of how convenience continues to undermine digital security.
In a world where billions of credentials are exposed every year, attackers don’t need advanced tactics to break into accounts protected by predictable passwords. They rely on automation, scale, and the knowledge that many users still prioritize simplicity over safety.
The solution isn’t fear—it’s awareness and action.
Use strong, unique passwords. Turn on multi-factor authentication. Monitor your accounts for breach exposure with tools like LeakDefend. Because in today’s threat landscape, the most common password in the world is also one of the most dangerous.
And if your password is still “123456,” now is the time to change it.