The T-Mobile data breach history is not defined by a single incident — but by a series of recurring security failures affecting tens of millions of customers. From 2018 through 2023, the telecom giant experienced multiple major breaches, exposing sensitive personal data including Social Security numbers, driver’s license information, phone numbers, and account details.
While data breaches have become increasingly common across industries, T-Mobile’s repeated incidents stand out. The pattern raises serious concerns about systemic weaknesses in cybersecurity governance, vendor oversight, and infrastructure security. Here’s a closer look at what happened, what data was exposed, and what customers should learn from it.
2018–2019: Early Warning Signs
T-Mobile’s breach troubles became public in 2018 when the company disclosed unauthorized access affecting approximately 2 million customers. Exposed data included names, billing ZIP codes, phone numbers, email addresses, and account numbers.
In 2019, another breach impacted prepaid customers after attackers gained access through a third-party vendor. While T-Mobile stated that financial data and Social Security numbers were not exposed in that incident, the recurring nature of breaches began to draw scrutiny from regulators and security experts.
These early events signaled deeper issues:
- Inadequate monitoring of internal systems
- Weak third-party security controls
- Delayed detection of unauthorized access
For many customers, these breaches marked the first time they realized how frequently telecom providers are targeted — and how valuable phone-linked identity data can be to criminals.
2020: Another 200,000 Accounts Compromised
In March 2020, T-Mobile disclosed that approximately 200,000 customer accounts were compromised after attackers exploited credential stuffing techniques. This type of attack uses usernames and passwords leaked from other breaches to gain access to accounts where users reused the same credentials.
The exposed data included phone numbers and account information. While smaller than other incidents, this breach highlighted a persistent problem: password reuse and inadequate safeguards against automated login attacks.
Credential stuffing remains one of the most common attack vectors today. This is why tools like LeakDefend are critical — they monitor your email addresses across known breaches so you can quickly change exposed passwords before attackers test them elsewhere.
2021: The Massive 76 Million Customer Breach
The most damaging incident in the T-Mobile data breach history occurred in August 2021. The company confirmed that a cyberattack exposed data belonging to approximately 76 million people, including both current and former customers.
The breach included highly sensitive information:
- Full names
- Dates of birth
- Social Security numbers
- Driver’s license and ID information
- IMEI and IMSI device identifiers
The attacker claimed to have accessed T-Mobile servers through a misconfigured router, gaining access to internal systems without detection for some time. The scale and sensitivity of the exposed data led to widespread criticism and regulatory scrutiny.
In 2022, T-Mobile agreed to a $350 million class-action settlement related to the 2021 breach — one of the largest data breach settlements in U.S. history. The company also committed to investing an additional $150 million in data security improvements.
Yet even that wasn’t the end of the story.
2022–2023: More Breaches, More Exposure
In January 2023, T-Mobile disclosed another breach impacting approximately 37 million customers. This time, attackers exploited a vulnerable API to access customer data over a period of weeks before detection.
Although the company stated that Social Security numbers and payment card information were not exposed in this particular incident, attackers did obtain:
- Names
- Billing addresses
- Email addresses
- Phone numbers
- Dates of birth
- Account details
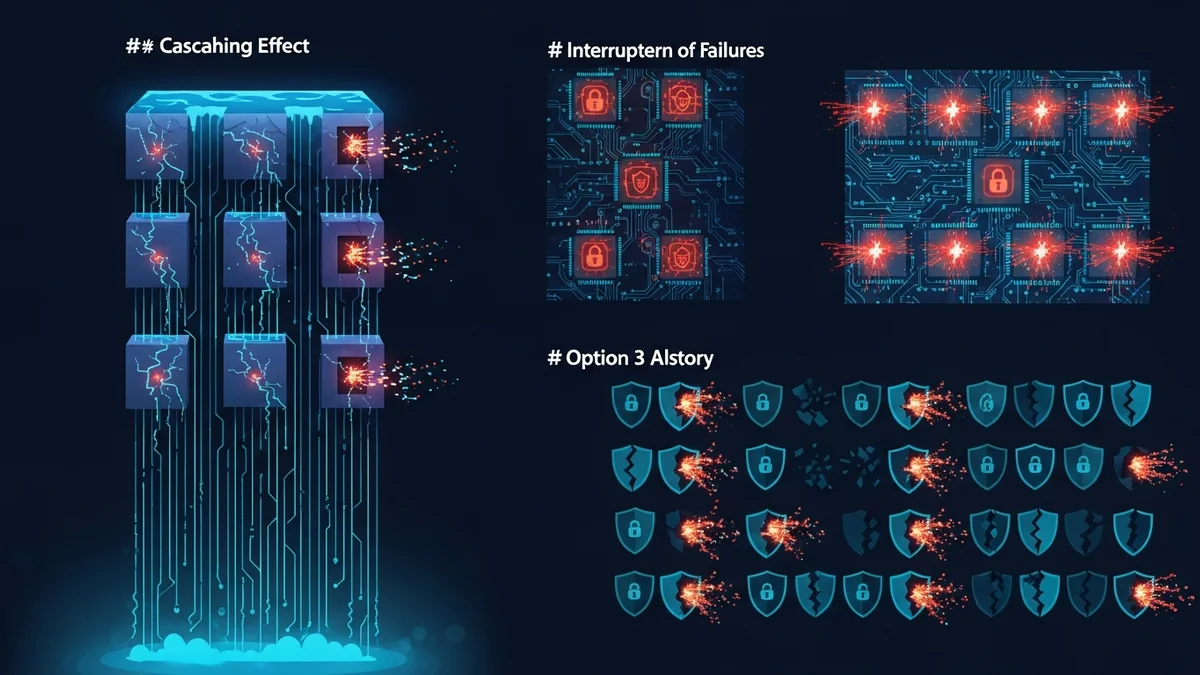
The repeated exposure of similar data fields demonstrates a troubling pattern: even after public scrutiny, settlements, and promised security investments, attackers continued to find exploitable weaknesses.
Why the T-Mobile Data Breach History Matters
Telecom providers hold uniquely sensitive data. Your phone number is tied to:
- Two-factor authentication codes
- Banking and financial services
- Social media accounts
- Government and healthcare portals
When telecom data is breached, attackers can attempt SIM-swapping attacks, identity theft, phishing campaigns, and account takeovers. Even partial datasets can significantly increase your exposure risk.
The T-Mobile data breach history illustrates several key lessons:
- Large companies are not immune. Brand recognition does not equal cybersecurity maturity.
- Repeated breaches signal systemic weaknesses. One incident may be bad luck; multiple incidents suggest structural issues.
- Consumers bear long-term risk. Stolen identity data can circulate on underground markets for years.
That’s why continuous monitoring matters. LeakDefend.com lets you check all your email addresses for free and alerts you if they appear in known breach databases — giving you the chance to act before criminals do.
What T-Mobile Customers Should Do Now
If you are a current or former T-Mobile customer, assume your data may have been exposed in at least one incident over the past several years. Proactive steps include:
- Use unique, complex passwords for every account
- Enable app-based two-factor authentication (not SMS when possible)
- Place a fraud alert or credit freeze if highly sensitive data was exposed
- Monitor your financial and telecom accounts for unusual activity
- Regularly check whether your email addresses appear in new breaches
Cybersecurity is no longer optional hygiene — it’s an ongoing process. Services like LeakDefend provide breach monitoring across multiple email addresses so you’re notified quickly when your credentials surface in newly disclosed incidents.
🔒 Check If Your Email Was Breached — Monitor up to 3 email addresses for free with LeakDefend. Start Your Free Trial →
Conclusion: A Case Study in Repeated Security Failures
The T-Mobile data breach history serves as a case study in how recurring cybersecurity lapses can erode trust. Despite settlements, public commitments, and infrastructure investments, the company experienced multiple large-scale breaches between 2018 and 2023.
For consumers, the lesson is clear: you cannot rely solely on corporations to safeguard your data. Even industry giants can fall victim to preventable vulnerabilities. Continuous monitoring, strong password practices, and proactive identity protection are essential defenses in today’s threat landscape.
Data breaches are no longer rare events — they are recurring realities. The difference between becoming a victim and staying protected often comes down to how quickly you detect exposure and respond.