The MOVEit hack is one of the most significant supply chain cyberattacks in recent history. In 2023, a single zero-day vulnerability in Progress Software’s MOVEit Transfer platform allowed attackers to compromise thousands of organizations worldwide — from government agencies to Fortune 500 companies. The scale and speed of exploitation stunned cybersecurity experts and highlighted a harsh reality: one vulnerable third-party system can ripple across entire industries.
Here’s how the MOVEit breach unfolded, why it became so widespread, and what it means for businesses and individuals trying to protect their data.
What Is MOVEit and Why Was It Targeted?
MOVEit Transfer is a managed file transfer (MFT) solution used by organizations to securely move sensitive data between systems. Governments, healthcare providers, financial institutions, and enterprises rely on it to transfer payroll data, personal information, contracts, and confidential business files.
In May 2023, the Clop ransomware group exploited a previously unknown SQL injection vulnerability in MOVEit Transfer. Because it was a zero-day vulnerability, there was no patch available when the attacks began. Attackers could remotely access MOVEit servers, extract stored data, and deploy web shells to maintain persistent access.
Rather than encrypting systems immediately, the attackers focused on mass data theft. This shift toward data exfiltration and extortion reflects a broader trend in ransomware operations: stealing first, threatening to leak later.
How One Vulnerability Scaled Into a Global Crisis
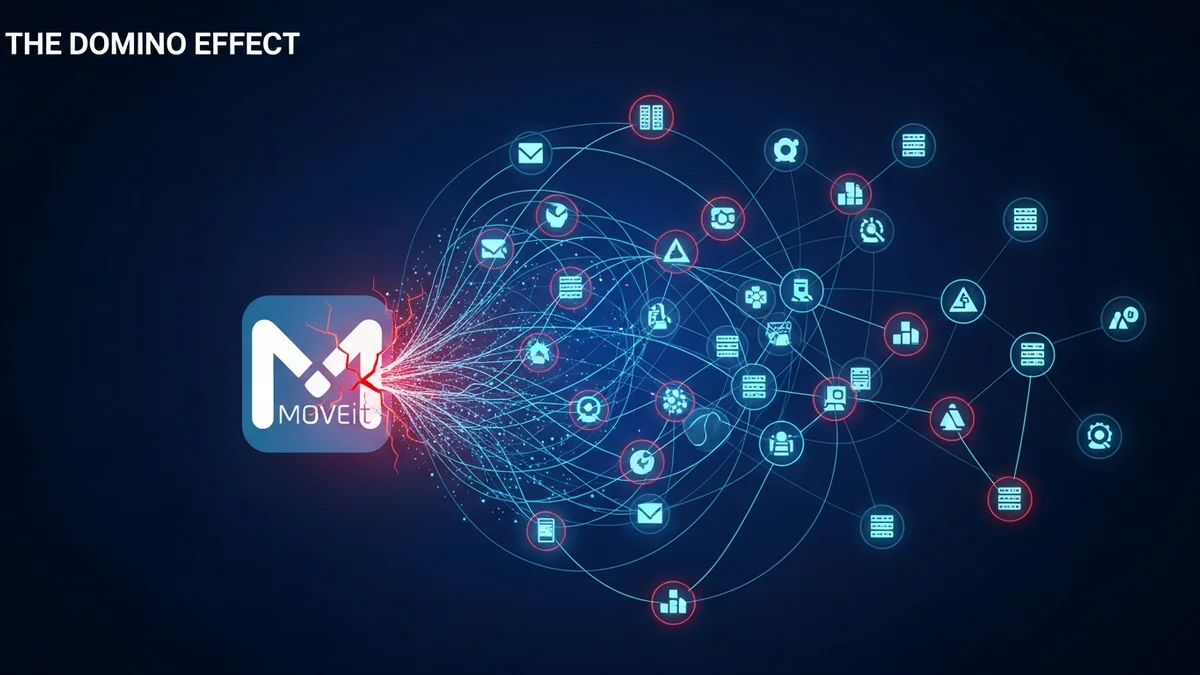
The true danger of the MOVEit hack wasn’t just the vulnerability itself — it was the interconnected nature of modern business systems.
Many organizations using MOVEit were service providers handling data on behalf of other companies. When one vendor was compromised, hundreds of downstream customers were affected. This created a cascading supply chain breach.
By late 2023, reports indicated:
- More than 2,500 organizations were impacted
- Over 90 million individuals had personal data exposed
- Victims included U.S. federal agencies, the BBC, British Airways, Shell, and multiple universities
For example, payroll provider Zellis was breached via MOVEit, which in turn exposed employee data from major UK companies. In the United States, government agencies such as the Department of Energy reported impacts through third-party vendors.
This pattern demonstrates a growing cybersecurity risk: organizations may have strong internal defenses but remain vulnerable through external partners.
What Data Was Exposed?
The MOVEit attacks primarily targeted stored files within compromised servers. Because MOVEit is often used for high-value transfers, the stolen data frequently included:
- Full names
- Home addresses
- Email addresses
- Dates of birth
- Social Security numbers or national IDs
- Payroll and financial information
Unlike password-only breaches, this type of exposure creates long-term identity theft risks. Social Security numbers and government IDs cannot simply be “reset” like a password.
For individuals, this means increased risk of phishing attacks, identity fraud, and financial scams. Tools like LeakDefend can monitor your email addresses for breach exposure and alert you if your data appears in known leaks, helping you react faster when incidents like MOVEit occur.
The Role of Clop and Modern Data Extortion
The Clop ransomware group has been active for years, but the MOVEit campaign marked a shift toward highly coordinated mass exploitation.
Instead of attacking organizations one at a time, Clop automated the scanning and exploitation of vulnerable MOVEit servers across the internet. Once they identified targets, they extracted data and later posted victim names on their leak site to pressure companies into paying.
This model reflects a larger trend in cybercrime:
- Exploit widely used enterprise software
- Steal large datasets quickly
- Extort victims through public exposure threats
Because no encryption was required, victims could not rely on backups alone. Even if systems were restored, stolen data remained in criminal hands.
Why the MOVEit Hack Matters for Every Organization
The MOVEit breach underscores several hard lessons:
- Zero-day vulnerabilities are inevitable. Even trusted vendors can harbor critical flaws.
- Supply chain risk is systemic. A vendor’s vulnerability becomes your vulnerability.
- Data minimization matters. Storing large volumes of sensitive data increases breach impact.
- Speed of patching is critical. Progress released patches quickly, but exploitation had already begun.
Organizations must maintain continuous third-party risk assessments, implement network segmentation, and monitor unusual file transfer activity. Regular vulnerability scanning and rapid patch deployment are no longer optional — they are foundational.
For individuals, breaches like MOVEit reinforce the importance of proactive monitoring. If your payroll provider, university, or healthcare provider is compromised, you may not know immediately. Services like LeakDefend.com let you check all your email addresses for free and receive alerts if your information appears in known breach datasets.
What You Should Do If You’re Affected
If you receive a notification that your data was involved in the MOVEit hack or a similar third-party breach, take these steps:
- Place a fraud alert or credit freeze if Social Security or financial data was exposed
- Change passwords on related accounts
- Enable multi-factor authentication everywhere possible
- Monitor bank accounts and credit reports closely
- Watch for targeted phishing emails referencing your employer or service provider
Because stolen data may circulate for years, ongoing monitoring is essential. Cybercriminals often wait months before launching secondary attacks using previously stolen information.
The Bigger Picture: A Warning for the Digital Economy
The MOVEit hack wasn’t just another breach — it was a wake-up call. A single vulnerability in a widely trusted file transfer system compromised thousands of organizations and tens of millions of people. It exposed the fragility of interconnected digital infrastructure.
As businesses increasingly rely on cloud platforms, managed services, and third-party software, supply chain security becomes one of the defining cybersecurity challenges of the decade.
No organization can eliminate risk entirely. But layered defenses, rapid patch management, vendor oversight, and personal data monitoring can significantly reduce impact.
The MOVEit breach proves that in cybersecurity, the weakest link is often outside your direct control. Staying informed — and actively monitoring your digital exposure — is no longer optional. It’s essential.